The flu isn’t the only health scare that’s going around this season. Two recently discovered computer chip vulnerabilities — ominously nicknamed Meltdown and Spectre — pose gigantic security threats to almost all modern computer processors, and you’re probably affected by both of them.
Most computer security vulnerabilities result from defects in software code, said Matt Tait, a cybersecurity fellow at UT-Austin’s Strauss Center for International Security and Law. Fixing these software defects is usually pretty simple, requiring the authors of the software to remove the bug by changing the code and then sending users a security update. Fixing Meltdown and Spectre will require a little more work because they prey on risks inherent to these microprocessors, including those from Intel, AMD and ARM.
“Computers are porous devices — it’s just how porous they are and how many holes we know they have in them,” computer science professor Warren Hunt said. “And this is a rather big hole and without mitigation, it’s quite large. It’s also, unfortunately, one that’s weirdly part of the silicon chip.”
Meltdown and Spectre sound pretty scary, and they are, especially because they are flaws in the actual hardware of the chip and not just a software issue. But there’s some good news — they weren’t purposefully engineered. Instead, they were the result of complex interactions between operating system security and modern processors, according to Tait.
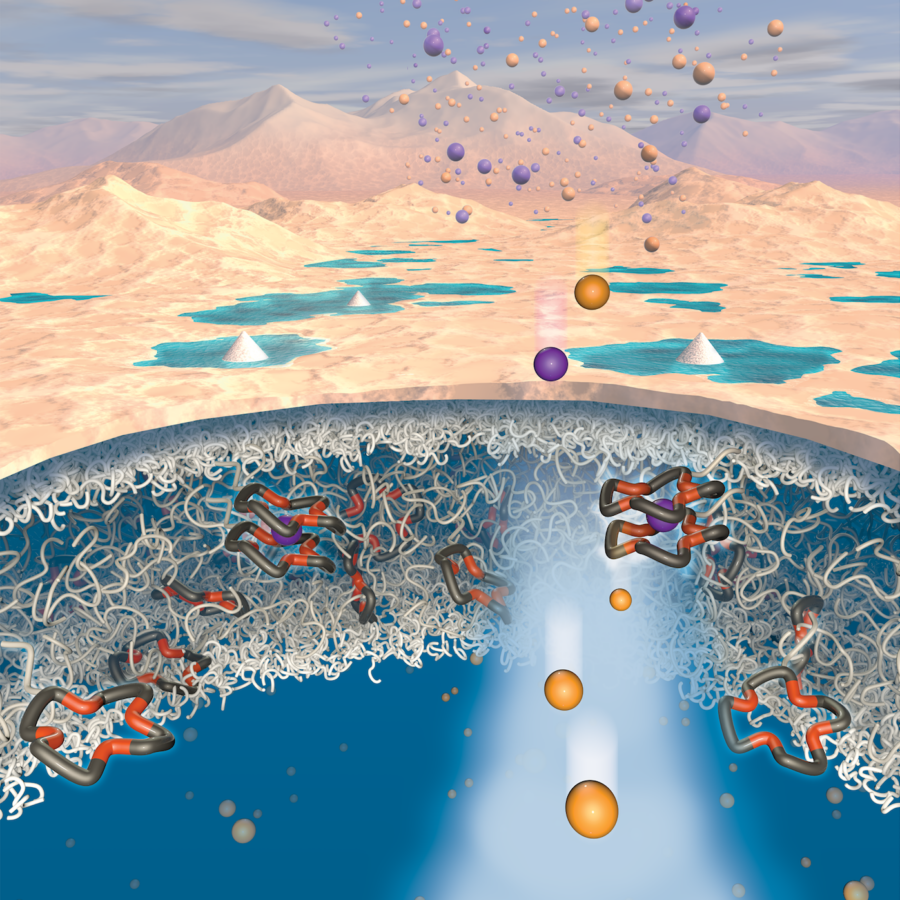
These two flaws allow information to be exfiltrated out of a computer or phone through indirect means, specifically through computer side-channels, Hunt said.
Computers perform work, and work requires energy. Any time you have an activity, there is some residual, observable result of it, Hunt explained. The more work that is being performed, the more energy that is required, and by measuring the amount of energy in use by the computer, you can get a sense of how hard the system is working.
For example, via these indirect means, you can measure the response speed of a computer processor to certain memory requests.
“You can see that some requests go fast and some go slow, and by doing that you can discern what was used to index into the structure,” Hunt said. “(You can find out) how long it takes to get something that, even though you can’t actually see the value, you can measure the time difference and (therefore) effectively find the value.”
This is a problem because of the way modern computer processors are optimized to run software quickly, according to Tait. The optimizations can interfere with security isolation techniques that work to keep data in different programs separate from each other.
“For example, an advert in a web browser should not be able to see data you are typing in a Microsoft Word document or the password you have typed to login to your computer,” Tait said.
“These performance optimizations can’t be fixed by a software update because they are present in the hardware, but the security isolation techniques can,” Tait said. “This means that all people need to do is install operating system updates on their laptops and phones, because this will update the operating system with new security isolation techniques that can work around the hardware problem.”
But getting rid of the problem completely is another feat entirely.
“Did all the people who had cars with a certain safety recall … immediately go sell their car? No, they (knew they were) living with a risk, some worse than others,” Hunt said. “These problems are either headaches or hassles or safety issues, but unfortunately, the one we have now is more on the order of the brakes randomly not working. It’s nothing short of replacing the entire brake system in this case.”
There are steps people can take to mitigate the risk posed by Meltdown and Spectre. Apple has come out with updates for iOS, macOS and Safari, and Microsoft has also provided firmware security patches for machines running Windows, but these aren’t permanent solutions.
“It’s likely that … new hardware (will be developed) that will substantially mitigate this problem, and then maybe some other clever people in two, three, four or five years will develop another one,” Hunt said. “It’s the way this works.”